
Short post to explain how to create a stealthy HTA file running without any window or taskbar mention. This can be used combined withe other techniques to create advanced payloads for redteaming/supply chain attacks.
License : Copyright Emeric Nasi (@EmericNasi), some rights reserved
This work is licensed under a Creative Commons Attribution 4.0 International License.
![]()
About
I wrote this short post to explain how to create a stealthy HTA file that launches without any window or taskbar mention.
An invisible HTA file can be used combined with other techniques to create advanced payloads for redteaming/supply chain attacks.
The goal of this post is not to describe what is an HTML Application or HTA.
If you don’t know what HTA are you can read the Introduction to HTML Applications
1. Some unsatisfying solutions:
When you google "hide hta files" you will find two different solutions, none of which are very satisfying:
- Minimizing the HTA window via WINDOWSTATE="minimize"
- Minimizing the HTA windows using via the script (ex window.resizeTo(0,0);)
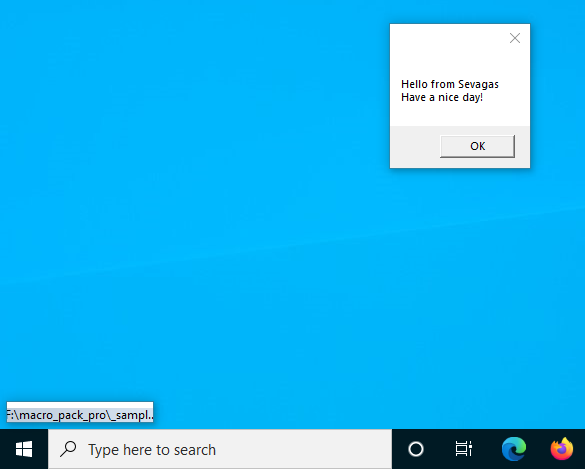
An example of HTA file using method 1 (a hello world):
The problem with WINDOWSTATE="minimize" is that a small UI with the path to script appear in the corner.
It is discrete but can be detected if the payload is running for some time.
Notice the message in the bottom left corner:
A better method consist into playing with the HTA window from the script itself.
If possible for example to use window.resizeTo to make the window collaps or use window.moveTo to move the HTA window out of the screen.
This method is better as there is no more small HTA UI in the corner. The problem, however is that there is a "glitch"; the HTA window appears very briefly before the script is applied.
This glitch could be considered suspicious in a redteam scenario, an attentive user could report it.
2. Best solution
The second proposition is the best but how to remove the glitch? Well it appear that the windows that pops briefly is the HTA windows and its borders.
I tested with various attributes and whats nice is that glitch disappears when you remove the borders. This can be done with the attribute BORDER="none"
So here is the best proposition to hide a running HTA file;
This way, the running HTA is totally invisible and there is no windows briefly appearing when its started.
This template is implemented in the latest versions of MacroPack community and MacroPack Pro which can be used to automatically generate weaponized HTA files.
3. Usage in redteam scenario
There are several interesting scenario where you can use an invisible HTA.
Using the HTA file format
Concerning HTA files themselves, you could spoof the extension using special Unicode characters such as described in this post.
For example, you could create an HTA file which seems to end in *.jpg so the target thinks its a picture.
Then, from the HTA script you can launch a decoy image so the user really thinks he has opened a picture.
The HTA script can be used to run any VBS payload on the computer, including shellcode injection payload using Win32 API via Office application com objects.
Using other file formats (polyglot self calling HTA)
A few years ago I wrote a post about some HTA nice properties (Hacking around HTA files).
A nice property of HTA is that its easy to create polyglot formats compatible with MSHTA.
I recommend you read the blog post it if you are now aware about that.
This way its possible to add VBS scripting capabilities to non VBscript formats such as LNK shortcuts, Windows help files, or Visual Studio Project files.
In all those case, the HTA part should run invisible to avoid suspicion
This can lead to the creation of complex payloads all in a single file. In the example below I trojan an existing shortcut pointing to notepad.exe with a special HTA Macro.
Here is what happens when someone double clicks on the short cut:
- LNK execute mshta on itself
- Embedded HTA script uses COM to launch Excel in background
- HTA script copies a VBA macro in the Excel memory (not persisted)
- The VBA macro is executed and use some Win32 API to execute a raw Meterpreter shellcode.
Finally
Note that there are plenty other ways to use regular HTA or HTA polyglot in red team scenario (web download, phishing, supply chain attack)
Going through those is out of the context of this short post, but it might be interesting to explore later.
I already wrote a post about advanced USB key phishing based on weaponized HTA you can find here.
Also note that all the advanced scenarios including decoy launch and HTA polyglot abuse are implemented in MacroPack Pro .
